In one of the most damaging cyberattacks of the war to date, Ukrainian military intelligence has reportedly breached the internal systems of Russia’s leading strategic bomber manufacturer, Tupolev. A Ukrainian source familiar with the operation described the scale of the breach as “total,” claiming, “There’s nothing secret left.”
Tupolev, a cornerstone of Russia’s military aviation industry, is responsible for the design and production of the country’s long-range bombers, including the Tu-95 “Bear,” the supersonic Tu-160 “Blackjack,” and the Tu-22M3 “Backfire.” These aircraft form a crucial part of Russia’s nuclear triad and have played key roles in the war against Ukraine, particularly in launching cruise missile strikes deep into Ukrainian territory.
According to sources within Ukrainian defense circles, the hack yielded a trove of sensitive documents. These include blueprints, weapons integration data, maintenance schedules, internal correspondence, and system vulnerabilities—information that, if verified, could be invaluable in countering Russian air capabilities. The exact date and method of the breach remain undisclosed, but officials suggest the operation was months in the making.

“This is not just a symbolic victory. This is a major operational breakthrough,” a Ukrainian military source said on condition of anonymity. “We now understand far more about how Russia’s strategic aviation functions—and how to disrupt it.”
The cyberattack reportedly targeted internal networks and data servers at Tupolev’s main facilities. Ukrainian officials claim the operation exposed years of technical development and testing data, as well as communications with the Russian Ministry of Defense. According to one source, the haul even includes records about supply chain weaknesses and production delays—issues that could compound Russia’s struggle to maintain its aging bomber fleet.
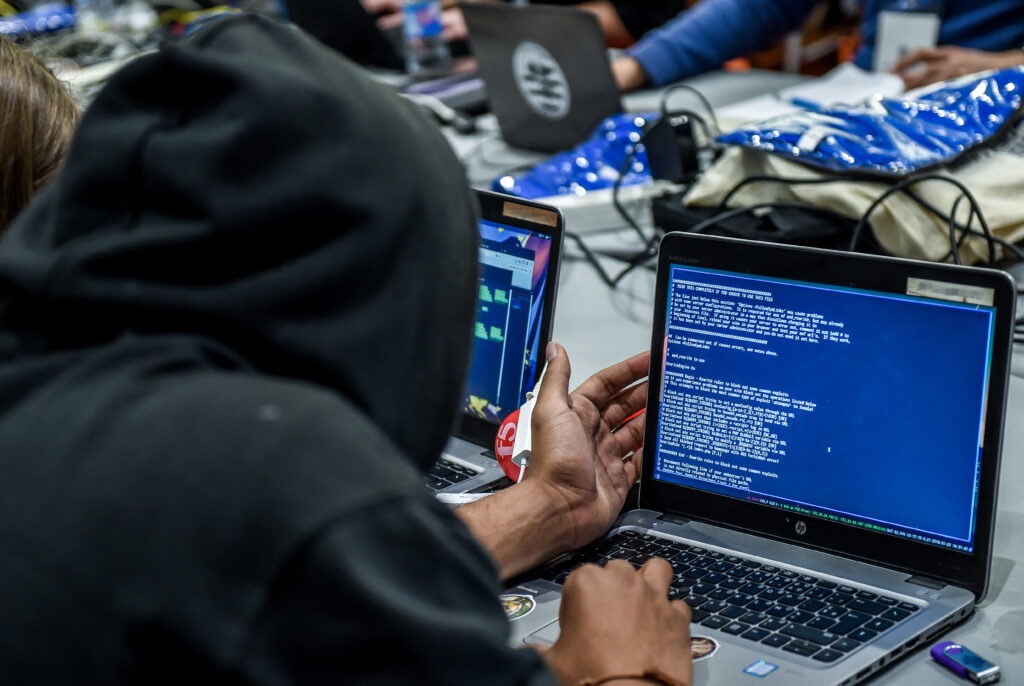
For Ukraine, this hack is the latest in a string of high-profile cyber operations aimed at undermining Russian military and industrial capabilities. Over the past year, Ukraine’s Security Service (SBU) and military intelligence directorate (GUR) have stepped up efforts to penetrate Russia’s defense infrastructure, previously targeting the Federal Air Transport Agency (Rosaviatsia) and military logistics databases. Each successful operation not only disrupts Russian activity but also bolsters Ukraine’s defensive planning.
In addition to the strategic implications, the psychological impact on the Russian defense sector could be significant. Tupolev is not just another defense contractor—it is a symbol of Soviet and Russian airpower, long associated with the country’s nuclear deterrence and global military reach. A breach of this magnitude casts serious doubt on Russia’s ability to secure its most sensitive military-industrial assets in the digital age.
The Kremlin has yet to issue an official statement on the breach. However, Russian state media have begun reporting increased security measures at various defense installations, and sources inside Moscow suggest a quiet internal review is already underway. There are concerns that the breach could trigger a broader internal purge or crackdown on perceived security lapses across the military-industrial complex.
Cybersecurity experts note that the scale of this breach—if verified—underscores the growing importance of cyber warfare in modern conflict. Unlike traditional military strikes, cyberattacks can expose secrets, erode trust, and damage complex systems without firing a shot. And as this incident illustrates, the digital battlefield can extend far beyond the front lines, deep into the heart of a nation’s strategic command.

While the long-term consequences of the Tupolev hack are still unfolding, Ukrainian officials are already signaling that more operations are on the horizon. “This is just the beginning,” the military source said. “Every system they rely on, we are watching. And we’re not stopping.”
As the Russia-Ukraine war continues to evolve, so too does the battlefield—no longer limited to tanks and trenches, but now deeply entrenched in cyberspace. And with each breach, the war for information becomes as vital as any territory.